USG20-VPN NAT does not work after router substitution
Options
FrancoCorbelli
Posts: 1  Freshman Member
Freshman Member

 Freshman Member
Freshman Member
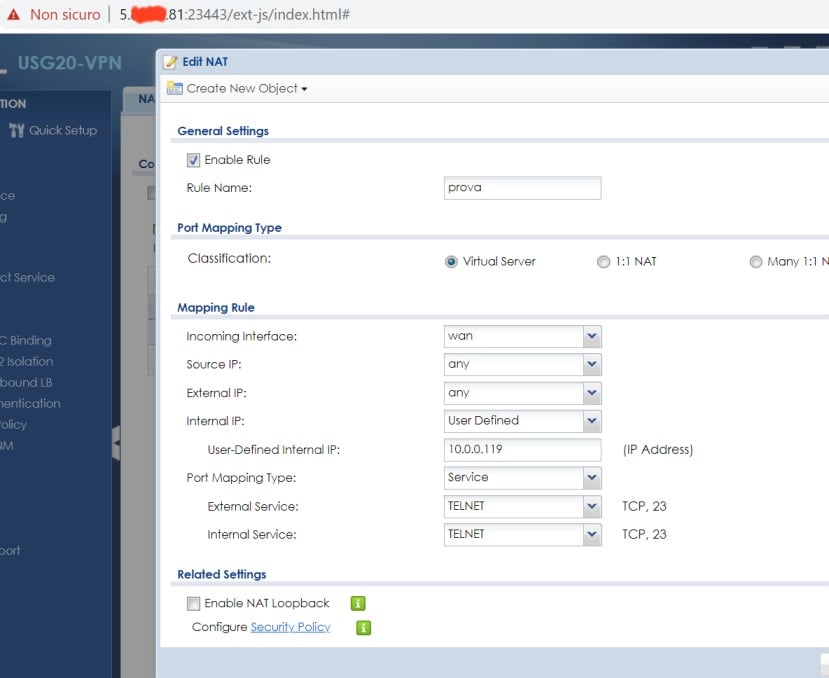
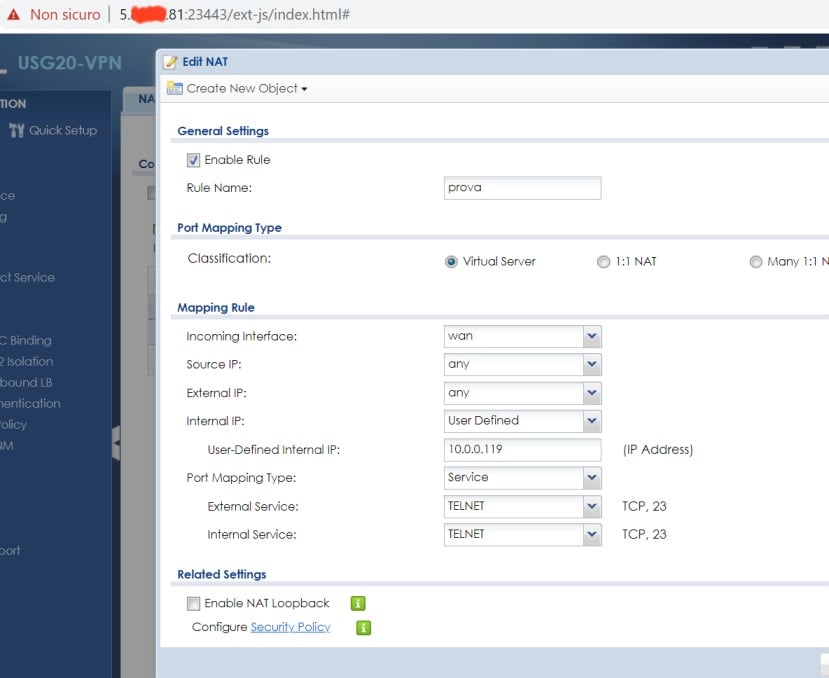
I am having difficulty activating a simple NAT on USG20 (firmware 4.62), after a VDSL router replacement.
The router have a public internet IP (5.x.y.81), and a LAN IP (192.168.0.251/24).
I cannot operate on the Vodafone router and, therefore, I must "trust" that a 1:1 NAT has been configured between all its ports to the USG (as requested).
The USG WAN port is 192.168.0.9/24 (default gateway of course 192.168.0.251), and the is LAN 10.0.0.248/24
On the LAN (via a switch) there are various servers, for my tests a NAS, with IP 10.0.0.119/24, gateway ANOTHER USG (10.0.0.254), various service (for test say 23 telnet)

I want a NAT from the router to the NAS, telnet 5.x.y.81 (from outside) should go to => 192.168.0.119:23
It sounds simple, but I doesen't work.
For testing purposes I can even keep the firewall (policy control) disabled.
It is possible to reach the https interface from Internet (https:5.x.y.81), and even FTP, SSH etc (ssh 5.x.y.81) of the USG (test configuration of course).
By verifying from the web console (of USG) it is possible to telnet 10.0.0.119 and log in, therefore the USG <=> NAS traffic should work
In theory, a NAT rule should be enough (and then the firewall rule but, as mentioned, for testing I can also leave it disabled)
I can reach the Zywall (even FTP, just for test, https etc), from Internet

USG can "speak" with the NAS, as it shoud be (telnet for test)

BUT, when I try telnet 5.x.y.81 (or whatever, ssh, https etc) => impossible.
By setting a specific policy (to be able to log) everything seems to actually arrive as expected, in this case from my external internet IP (nas1 = 10.0.0.119)
The same problem occurs for services other than telnet (ssh etc).
Thanks for any helps

The router have a public internet IP (5.x.y.81), and a LAN IP (192.168.0.251/24).
I cannot operate on the Vodafone router and, therefore, I must "trust" that a 1:1 NAT has been configured between all its ports to the USG (as requested).
The USG WAN port is 192.168.0.9/24 (default gateway of course 192.168.0.251), and the is LAN 10.0.0.248/24
On the LAN (via a switch) there are various servers, for my tests a NAS, with IP 10.0.0.119/24, gateway ANOTHER USG (10.0.0.254), various service (for test say 23 telnet)

I want a NAT from the router to the NAS, telnet 5.x.y.81 (from outside) should go to => 192.168.0.119:23
It sounds simple, but I doesen't work.
For testing purposes I can even keep the firewall (policy control) disabled.
It is possible to reach the https interface from Internet (https:5.x.y.81), and even FTP, SSH etc (ssh 5.x.y.81) of the USG (test configuration of course).
By verifying from the web console (of USG) it is possible to telnet 10.0.0.119 and log in, therefore the USG <=> NAS traffic should work
In theory, a NAT rule should be enough (and then the firewall rule but, as mentioned, for testing I can also leave it disabled)
I can reach the Zywall (even FTP, just for test, https etc), from Internet

USG can "speak" with the NAS, as it shoud be (telnet for test)

BUT, when I try telnet 5.x.y.81 (or whatever, ssh, https etc) => impossible.
By setting a specific policy (to be able to log) everything seems to actually arrive as expected, in this case from my external internet IP (nas1 = 10.0.0.119)
The same problem occurs for services other than telnet (ssh etc).
Thanks for any helps

0
All Replies
-
Hello @FrancoCorbelliMy guess is that your Vodafone router is not passing telnet through.A way to prove this would be to put a PC running Wireshark ( https://wireshark.com/index.php?/ ) between your Vodafone router and your USG20-VPN device or turn on the Firewall on your USG20-VPN device to block telnet and have it log the connection.- if you cannot see it in the firewall log, then your Vodafone router is not passing telent connections through from the Internet.If the above hypothesis is true, then you may need to look at using the VPN capabilities of your USG20-VPN, see section 5 of the user guide available at https://www.zyxel.com/us/en/support/download_landing/product/usg20_vpn_usg20w_vpn_22.shtml?c=us&l=en&pid=20151111155041&tab=User_s_Guide&pname=USG20-VPN/USG20W-VPNOnce you have an IPSEC tunnel set-up, then you will be able to run telnet and other protocols over the top of it.Also, is the Vodafone router necessary and a Vodafone requirement? If it is not, then maybe your USG20-VPN device be your broadband router connecting to Vodafone ISP.- it would give you more control.Kind regards,Tony
0 -
Hello @FrancoCorbelliAnd if the public router was the last thing changed, then it is probably the current root cause of your issues.But telnet is not secure over the Internet, because the user name and password are sent as clear text, so it would be more secure for your NAS if you were able to set up a VPN with encryption such as SSL or IPSEC.Kind regards,Tony
0 -
@tonygibbs16, thanks for the instruction.Hi @FrancoCorbelli,Welcome to Zyxel community.
 You also can capture on USG20 wan interface to check if the packets reach USG wan interface.Assume you still cannot see telnet packet comes to USG20 Wan interface, then it could be blocked by ISP router.
You also can capture on USG20 wan interface to check if the packets reach USG wan interface.Assume you still cannot see telnet packet comes to USG20 Wan interface, then it could be blocked by ISP router.
CLIRouter> packet-trace interface wan1 extension-filter port 23
Web GUI
MAINTENANCE > Diagnostics > Packets Capture 1
1
Categories
- All Categories
- 442 Beta Program
- 3K Nebula
- 229 Nebula Ideas
- 130 Nebula Status and Incidents
- 6.6K Security
- 661 USG FLEX H Series
- 359 Security Ideas
- 1.8K Switch
- 86 Switch Ideas
- 1.4K Wireless
- 56 Wireless Ideas
- 7.1K Consumer Product
- 305 Service & License
- 497 News and Release
- 95 Security Advisories
- 31 Education Center
- 10 [Campaign] Zyxel Network Detective
- 5K FAQ
- 34 Documents
- 89 About Community
- 110 Security Highlight
 Guru Member
Guru Member



 Zyxel Employee
Zyxel Employee






