SSL WEB Application
Bad Gateway
The proxy server received an invalid
response from an upstream server.
Additionally, a 400 Bad Request error was encountered while trying to use an ErrorDocument to handle the request.
In the log file I see only this:
7 2019-04-26 11:18:13 info SSL VPN web application MYTomcatApp has been accessed. sent=958 rcvd=141 [count=4]
8 2019-04-26 11:17:54 info SSL VPN User user1 has accessed web application MYTomcatApp [count=2]
Accepted Solution
-
Check the NAT rule and then the Policy Control rules:
1) Create Service Objects for each External and Internal port you need ( one for 44443 and one for 9099 ) under Configuration-> Object -> Service.
2) Under your NAT rule use the new object ( for port 44443 ) as your External Port and then the other object ( for port 9099 ) as your internal port. Ensure the source/destination interfaces and source/destination address ranges are correct for your network as well. Save the NAT rule.
3) Now you want to check your Policy Rules under Configuration->Security Policy->Policy Control and/or create a rule there so that the firewall can handle the non standard port as it deals with the those inbound requests. Create a new rule from WAN as the source interface and your internal interface as your destination. External port will be the object you created for port 44443 and the internal port you would select the object you created for port 9099. Save the rule
These steps will completely allow the forwarding of all the traffic occurring on the external to your internal application.
If the ZYWALL or USG is interfering with the SSL of your custom web site in any way, it's because you've possibly configured the built-in ZYWALL SSL service to handle those ports, which is not what I believe you are trying to do.
5
All Replies
-
Hi @RafYour configuration should be correct.For resolving this issue I will send you private message to get more detail information.0
-
Hi @Raf
The revers proxy mode is coding by Java. Since Java have some of security concern.
So many browser may not support any more.
We would like to suggest you use full tunnel mode(SecuExtender) for this scenario.
0 -
Yes, I do .ThanksRaffaele0
-
Check the NAT rule and then the Policy Control rules:
1) Create Service Objects for each External and Internal port you need ( one for 44443 and one for 9099 ) under Configuration-> Object -> Service.
2) Under your NAT rule use the new object ( for port 44443 ) as your External Port and then the other object ( for port 9099 ) as your internal port. Ensure the source/destination interfaces and source/destination address ranges are correct for your network as well. Save the NAT rule.
3) Now you want to check your Policy Rules under Configuration->Security Policy->Policy Control and/or create a rule there so that the firewall can handle the non standard port as it deals with the those inbound requests. Create a new rule from WAN as the source interface and your internal interface as your destination. External port will be the object you created for port 44443 and the internal port you would select the object you created for port 9099. Save the rule
These steps will completely allow the forwarding of all the traffic occurring on the external to your internal application.
If the ZYWALL or USG is interfering with the SSL of your custom web site in any way, it's because you've possibly configured the built-in ZYWALL SSL service to handle those ports, which is not what I believe you are trying to do.
5 -
Hi,
we are currently facing the same problem but we can't solve it, can you please tell us the procedure?
Thank you
0 -
Hi @ADIATIC
As @Zyxel_Stanley previous mentioned
We would like to suggest you use full tunnel mode(SecuExtender) for this scenario.
By using SecuExtender, you can build up tunnel to the device, then you can login to your server.
Here is the step to setup SSL VPN on USG with SecuExtender to login.
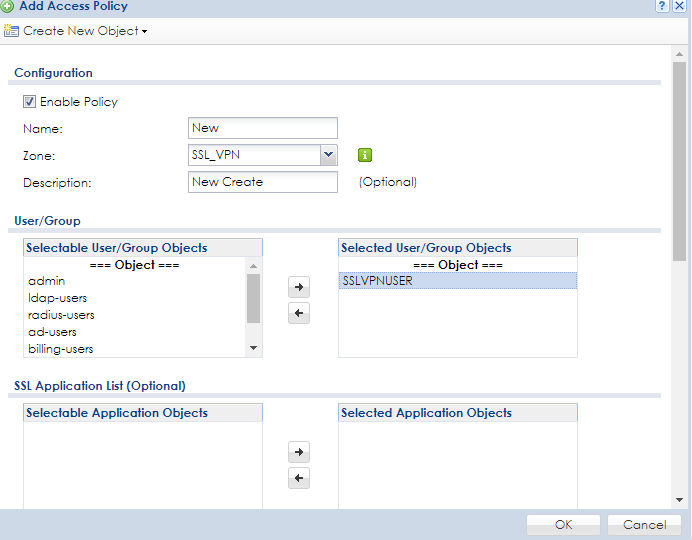
Go to Configuration > VPN > SSL VPN > Access Privilege > Add SSL VPN rule
Add user for SSL VPN
Add IP range for SSL VPN
Select User/Group
Enable Full Tunnel Mode for SSLVPN tunnel
Assign IP Pool for SSL VPN rule
Select the Network to allow user to access.
Test result
0 -
thanks, I already got SecuExtender to work 100% but I thought the idea for SSL applications was that you could add a user in the router to access in internal website without the SecuExtender. E.g. For instance, allow a client to access a bug tracking system internal to your network...?
Thaks, JSA0 -
Hi @SyoSilIT,If you're using SecuExtender (full tunnel mode) to establish SSL VPN to USG/ZyWALL, you don't need to configure SSL application.0
-
Agree but maybe I am on a computer where I cannot run the full SSL VPN application then this feature would be very handy. In the scenario that I am in then I cannot run the SSL VPN in full tunnel mode or do SSH or anything. This feature would solve my problems but it seems like it has been left behind for years and it is not updated to meet the standards of current browsers. Why not just remove it?0
Categories
- All Categories
- 442 Beta Program
- 2.9K Nebula
- 222 Nebula Ideas
- 129 Nebula Status and Incidents
- 6.5K Security
- 617 USG FLEX H Series
- 347 Security Ideas
- 1.7K Switch
- 84 Switch Ideas
- 1.4K Wireless
- 53 Wireless Ideas
- 7K Consumer Product
- 298 Service & License
- 485 News and Release
- 92 Security Advisories
- 31 Education Center
- 10 [Campaign] Zyxel Network Detective
- 4.8K FAQ
- 34 Documents
- 88 About Community
- 105 Security Highlight
 Freshman Member
Freshman Member



 Zyxel Employee
Zyxel Employee