Zyxel GS1920 + USG-20 problem
Hi all,
After ~10 hours of copilot-assisted, unsuccesful home network configuration effort it is time to call for help.
My setup and what I have done so far:
Network setup
- ISP provided internet device
- Firewall: Zyxell USG20-VPN
- Switch: Zyxell GS1920-24HPv2
- APs: 4 x UniFi U6+ PoE
ISP connected to firewall WAN port. From firewall LAN1 to swith LAN1 port.
Firewall (bought as used devide):
- Power up, factory reset
- Successful login to 192.168.1.1 by connecting pc to LAN2
- Firware update ⇒ ok
- Check internet connectivity ⇒ ok
- Otherwise factory default settings
Switch (bought as new recently):
Idea is to create:
VLAN10 (and “Main WiFI”) for PCs and other personal devices.
VLAN20 (and “Guest WiFi”) for PoE cameras, household appliances, etc.
Keep VLAN20 isolated from VLAN10
Started with factory reset and then did the following:
- Set PC to 192.168.1.3, connect with default admin PW ⇒ ok
- Change default admin pw, default SNMP community keys
- Create VLAN10 and VLAN20. Port settings:
- Port 1 (from firewall): VLAN10 fixed, untagged. VLAN20 fixed, tagged
- Port 2-5 (for U6+ APs): VLAN10 fixed, tagged. VLAN20 fixed, tagged
- Ports 6-13 (for PCs, etc.): VLAN10 fixed, untagged. VLAN20 forbidden
- Ports 14-24 (house devices): VLAN10 forbidden. VLAN20 fixed, untagged.
- Further settings:
- Ports 1-13 PVID: 10
- Ports 14-24 PVID: 20
- Ports 1-5 VLAN Trunking ON, otherwise off (this is current state, started without any ports trunking ON - not sure if this is relevant)
- From SYSTEM > IP SETUP, changed switch default management IP address to 192.168.10.1 and VID 10
- Deactivate VLAN1 ⇒ Successfully access management portal with PC set to 192.168.10.3
- Changed PC (in LAN port 6) to obtain IP address automatically. It gets 192.168.1.33 from firewall. Internet works perfectly!
- Test PC in VLAN20 ports. Internet does not work. I think I tried all combinations of port 1 VLAN settings (tagged / untagged, trunk / non-trunk). Still internet does not work with VLAN20 ports. “PROBLEM 1”
Next tried to set up "Main WiFi" WiFi despite issues with VLAN20.
- Installed UniFi network server on PC and used http://127.0.0.1:8080/ for accessing UniFi Network tool
- Connected one AP to port 2. Device appears for adoption, shows IP address 192.168.1.36 but gives “Connection interrupted” error message. Not able to continue setup. I have tried factory reset. “PROBLEM 2”
I did some network installations as a hobby some 15 years ago, but have lost most of the knowledge from my brain, so I would highly appreciate simple instructions.
What could be wrong with my VLAN10 / VLAN20 setup, why I cannot connect internet with VLAN20?
What could be blocking U6+ access points?
Thank you in advance! :)
All Replies
-
Hi @Henrik458,
Here are some hints for you:
- Please make sure the firewall port you connect with the switch is LAN 1 of the LAN 2 group.
- Please ensure your VLAN configuration is correctly configured with the correct LAN group. EX. You connect the LAN 1 group port to the switch. Your VLAN 20 interface should belong to LAN 1 group.
- AP issue: Please check your AP's management interface setting. Not sure if it needs to be configured tagged or untagged.
- VLAN trunking is no need currently since you only have two VLAN in your network. You can enable it when you have many VLAN in your network.
If you still need other help, please share your port settings and LAN configuration with us. This issue is more
Zyxel Melen0 -
Many ways to go about this here is one way
LAN1 P3 (I think) and port role P3 with P4
You can connect P4 to a PC and P3 to switch of port 1
You should be able to connect to switch GUI
Make VLAN 10 and 20 on USG with DHCP and there subnets also make zones for VLAN10 and VLAN20
Have VLAN 1 fixed for port 1 and Forbidden on all other ports with port 1 PVID 1
Make VLAN20 on switch fixed 2-5 and 14-24 with port 1 fixed and tag and ports 2-5 14-24 PVID 20 ports 6-13 Forbidden
The AP will be connected as untag for VLAN20
To connect to your AP's firewall rule LAN1 to VLAN20
Make VLAN10 on switch 6-13 fixed with PVID 10 on ports 6-13 port 1 fixed and tag port 2-5 and 14-24 Forbidden have ports 2-5 fixed and tag on VLAN10 make SSID for VLAN100 -
Thank you both for sharing ideas! Half way there, situation currently:
VLAN10: problems
VLAN20: both wired devices and guest WiFi work greatIn firewall settings, I have now identical setup for both VLAN10 and VLAN20:
For VLAN20 the same, but VLAN ID 20 and IP range 192.168.20.X.
I have tried VLAN10 also in LAN1 zone.Switch:
Problem currently:
- VLAN10 devices will get 192.168.1.X IP instead of 192.168.10.X. Internet connectivity however ok
- VLAN20 devices will get 192.168.20.X and all work ok
I don't understand how this is possible. If firewall would assign the IP for VLAN10 devices, one would think it should be 192.168.2.X given I have set VLAN10 to LAN2 zone?
When enabling VLAN1 and having switch port 1 to firewall as untagged and PVID 1 (as per Peter UK's suggestion), and changing port 1 as tagged for VLAN10, then devices will get 192.168.10.X address, but internet stops working (also tested pinging google.com or 8.8.8.8, no luck) and WiFi devices do not connect to the "main WiFi".
When again changing port 1 as fixed for VLAN10, wired devives work ok in 192.168.1.X space but WiFi devices still do not connect.
I have tried adding Policy control rules making sure LAN1 & LAN2 to wan is always allowed, and tried to define Policy route as well to manually allow VLAN10 to any destination, next hop being wan. Nothing helps, somehow problem persists on VLAN10 devices.
Any further suggestions, anyone?
Wife is out of the opinion this hobby is taking too much time lately already …0 -
Well VLAN10 is only correct if you fixed and tag port 1 to get a IP 192.168.10.X from the DHCP so thats working you then need Policy control from LAN2 to WAN
have you set the PVID correctly?
on VLAN 10 ports 2-5 fixed and tag
0 -
Thanks again for advice!
What I did:
- VLAN10 fixed and tag port 1 ⇒ IP 192.168.10.100, no internet
- Added policy control LAN2 to WAN allow ⇒ no impactNext I decided to adjust VLAN10 in firewall settings, changed IP range to start from 192.168.10.50 (instead of 100 previously). PC connected to VLAN10 would still get IP of 192.168.10.100, which was strange in my opinion.
Then changed VLAN10 to IP 192.168.11.1 with IP range starting from 192.168.11.50 ⇒ VLAN10 PC gets 192.168.11.50 and internet ok!
So by accident it now kind of works, but I don't understand what happened. Some kind of conflict somewhere? Any guess?Will test the wifi still later.
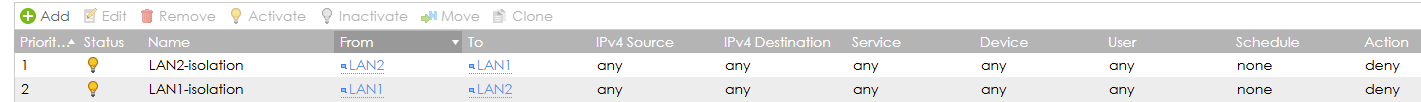
Isolation between VLAN10 and VLAN20 does not however still work. I changed VLAN10 back to LAN1 zone in firewall (VLAN20 LAN2). Then created following Policy Controls:
I'm still able to ping 192.168.20.1 with my VLAN10 PC. I suppose this should not be the case if isolation would work. Any ideas how to implement this?
0 -
Do you have another router that the WAN of the USG is connected too? maybe it has 192.168.10.0/24?
So what zone is set for VLAN10 and VLAN20?
0 -
Problem solved! Thanks for support.
I reached out to my ISP to check what kind of a device it is I have, and where USG is connected to. They said it is in bridge mode and should not conflict.
Today I however realized I had set the VLAN10 to 192.168.10.1 in firewall and the switch default management IP address was also 192.168.10.1. Changed the latter to 192.168.10.2 and now also VLAN10 works perfect. 🤦♂️
0
Categories
- All Categories
- 442 Beta Program
- 3K Nebula
- 228 Nebula Ideas
- 130 Nebula Status and Incidents
- 6.6K Security
- 648 USG FLEX H Series
- 357 Security Ideas
- 1.8K Switch
- 86 Switch Ideas
- 1.4K Wireless
- 55 Wireless Ideas
- 7.1K Consumer Product
- 304 Service & License
- 496 News and Release
- 93 Security Advisories
- 31 Education Center
- 10 [Campaign] Zyxel Network Detective
- 5K FAQ
- 34 Documents
- 89 About Community
- 110 Security Highlight
 Freshman Member
Freshman Member
 Zyxel Employee
Zyxel Employee



 Guru Member
Guru Member