How to Configure 802.1x to Secure the Wireless Environment with an External LDAP Server?
 Zyxel Employee
Zyxel Employee


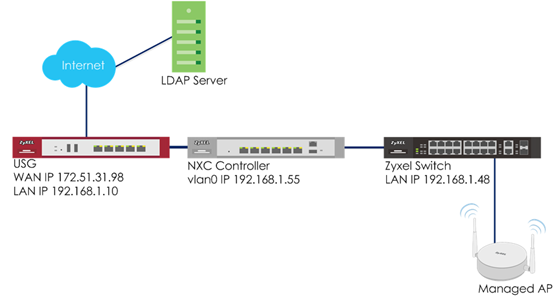
The example instructs how to set up the NXC controller with an external LDAP server. When the station wants to connect with the AP, you can use an AAA server to provide access control to your network. In this example, the LDAP server is external but not embedded in NXC controller, and the controller is already set to use the LDAP server for authentication.
Configure LDAP Server Setting
1 Go to CONFIGURATION > Object > AAA Server > LDAP, click #1 ldap, and then click Edit to edit the LDAP server’s information.
2 In Server Settings, enter Server Address. Here use 10.253.31.239 as the example. Go to LDAP server to check Base DN and Bind DN.
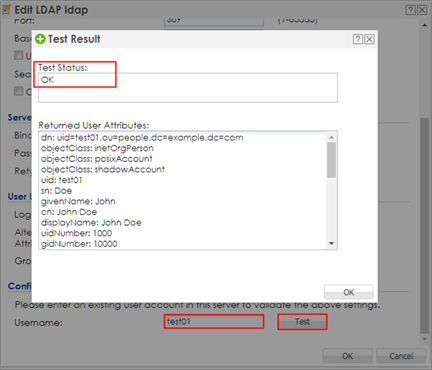
3 After finishing the configuration, enter administrator as the Username and click Test in Configuration Validation.
4 Go to CONFIGURATION > Object > Auth. Method. Select default method, and click Edit. Select the LDAP server you create. Click OK.
Configure AP Profile
1 Configure AP profile to use 802.1x authentication that user needs to log in with their ID and Password when connecting to AP’s SSID. Go to CONFIGURATION > Object > AP Profile > SSID > Security List, click Add to add security for 802.1x.
In General Settings, enter the Profile Name and change Security Mode to wpa2.
In Radius Settings, select Internal and it means the authentication needs NXC to communicate with external LDAP server.
In Authentication Settings, select 802.1x and Auth. Method is default. Click OK.
2 Go to CONFIGURATION > Object > AP Profile > SSID > SSID List, click add to add a SSID for the connection with 802.1x security. Key in the Profile Name and SSID, and change Security Profile to LDAP which you configured in step1. Click OK to save.
3 Go to CONFIGURATION > Wireless > AP Management > AP Group, select the default AP profile and edit. Select LDAPtest in the SSID Profile. Click Override Member AP Setting to apply the SSID to the AP and click Yes in the pop-up window. Click OK.
Test the Result
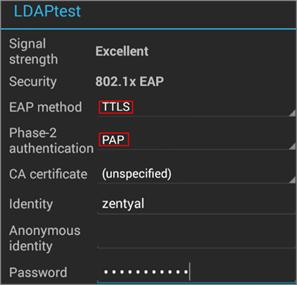
1 The LDAP can be use in Android phone for authentication. When connecting to the SSID, the EAP method is set to TTLS, and Phase-2 authentication is PAP. Enter the user ID and password to connect. The station and AP connected with correct ID and password.
What Could Go Wrong
1 The Radius server type is always internal in CONFIGURATION > Object > AP Profile > SSID > Security List because LDAP is not able to be used as the authentication server. It does not support external for LDAP server.
Categories
- All Categories
- 442 Beta Program
- 3K Nebula
- 228 Nebula Ideas
- 130 Nebula Status and Incidents
- 6.6K Security
- 643 USG FLEX H Series
- 357 Security Ideas
- 1.8K Switch
- 86 Switch Ideas
- 1.4K Wireless
- 54 Wireless Ideas
- 7K Consumer Product
- 303 Service & License
- 496 News and Release
- 93 Security Advisories
- 31 Education Center
- 10 [Campaign] Zyxel Network Detective
- 4.9K FAQ
- 34 Documents
- 89 About Community
- 110 Security Highlight