[2026 April Tips & Tricks] Collaborative Detection & Response: The New Front Line of Defense
 Zyxel Employee
Zyxel Employee
A Race Against Time and Limited Resources
For Managed Service Providers (MSPs), managing the modern threat landscape across multiple clients is a relentless, 24/7 adversary. As your clients embrace decentralized workforces, they introduce a rapidly expanding attack surface. Because most businesses cannot retain the high-level security expertise required to defend themselves, they rely entirely on your MSP team.
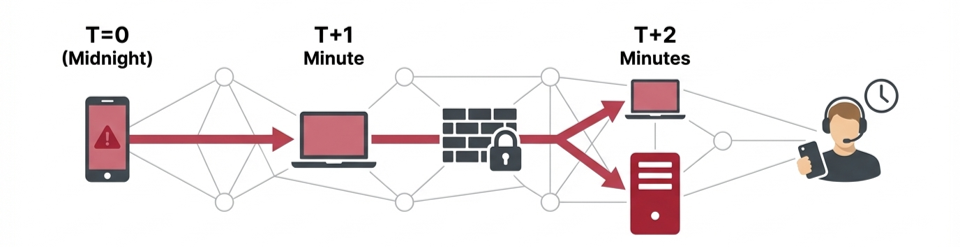
When a breach occurs at a client's site in the dead of night, the immediate infection is only half the battle. The true danger lies in lateral movement. Because most modern threats spread client-to-client within the same subnet or VLAN, a compromise can jump from a single smartphone to a critical server before your MSP helpdesk even receives the alert. If your team's defense strategy relies on manual intervention across distributed client networks, you have already lost the race.
Stay Ahead of Cyberthreats with Collaborative Detection & Response (CDR)
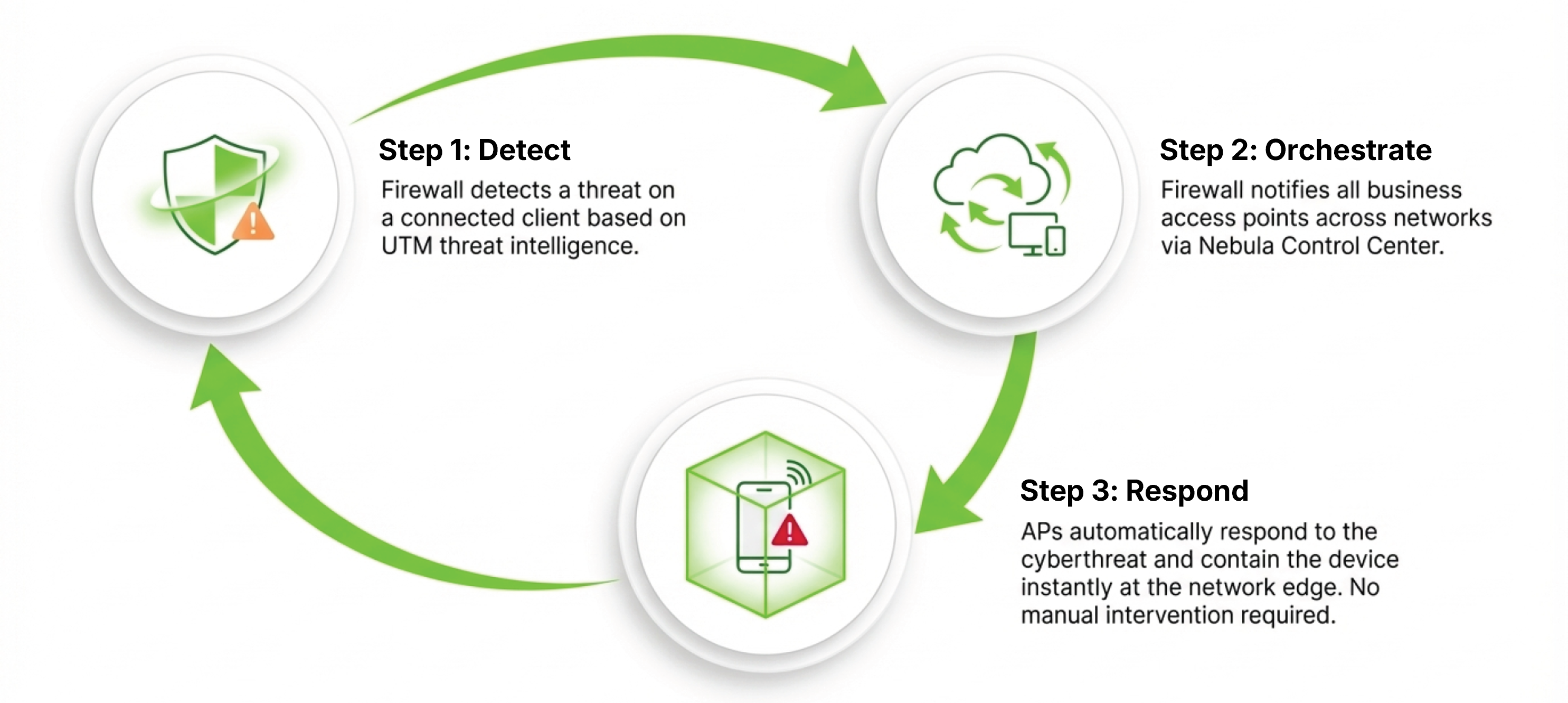
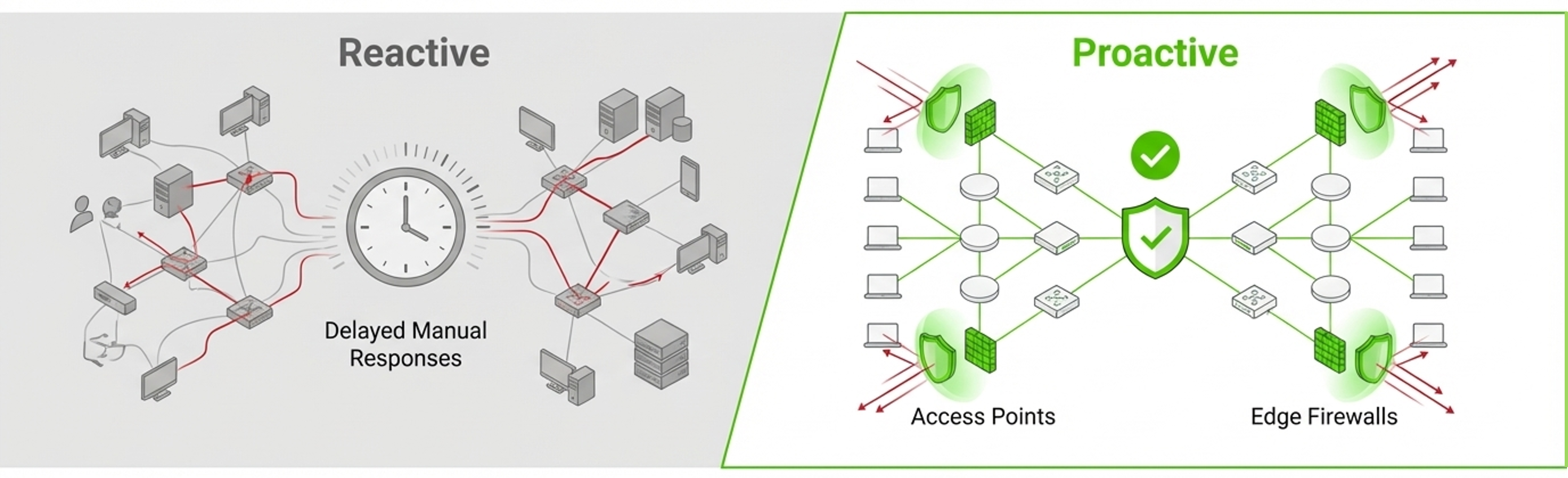
To protect complex organizational workloads and modern workplaces, security must move from a reactive posture to an automated one. We need systems that don't just "see" a threat but act on it instantly.
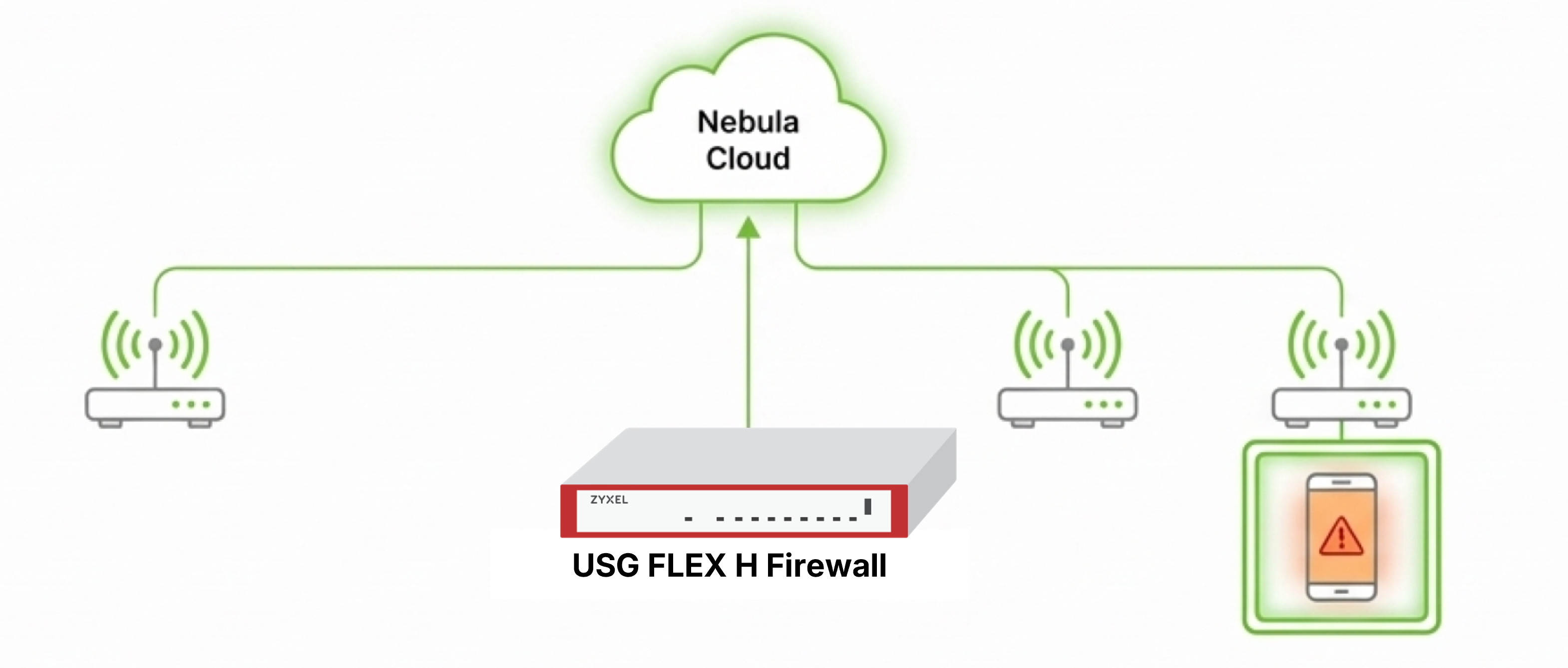
Collaborative Detection & Response (CDR) integrates Nebula firewalls and Nebula access points(APs) to deliver automated threat responses and mitigate risks. It transforms a collection of isolated hardware into a responsive, defensive ecosystem capable of containing threats at the moment of discovery—right at the network edge.
How CDR Protects the Network Edge
Traditional security models rely heavily on the firewall to act as a gatekeeper, but once a threat moves past the gateway, the internal network is often vulnerable. CDR moves protection to the access layer. This technology is supported by the USG FLEX H series firewalls, which serve as the "brains" of the operation.
When these firewalls detect an anomaly, they instantly sync with the Nebula Control Center (NCC). The NCC then pushes an automated response policy to all Nebula APs, containing the compromised device at the network edge. By pushing containment down to the access layer (Nebula APs), the system prevents malicious traffic from being broadcast to other clients in the same subnet or VLAN. This localized isolation ensures that one infected device cannot compromise the integrity of the entire corporate VLAN.
Understanding Alert, Block, and Quarantine
CDR provides three distinct containment actions, allowing MSPs to tailor their response to the specific needs of the client's workplace and workforce:
Containment Action | Device Supported | Network Action | End-User Experience |
|---|---|---|---|
🔔Alert | Firewall | Nebula is sending an alert email | Admin receives alert email; user unaware |
🚫Block | Firewall & AP | Traffic dropped & redirected to a block page | The user sees a "Limited Network Access" warning in the browser. |
🛡️Quarantine | AP | Dynamic VLAN assignment actively isolates the client | Client disconnected, receiving quarantine VLAN IP upon reconnection, seeing “Limited Network Access” warning in browser. |
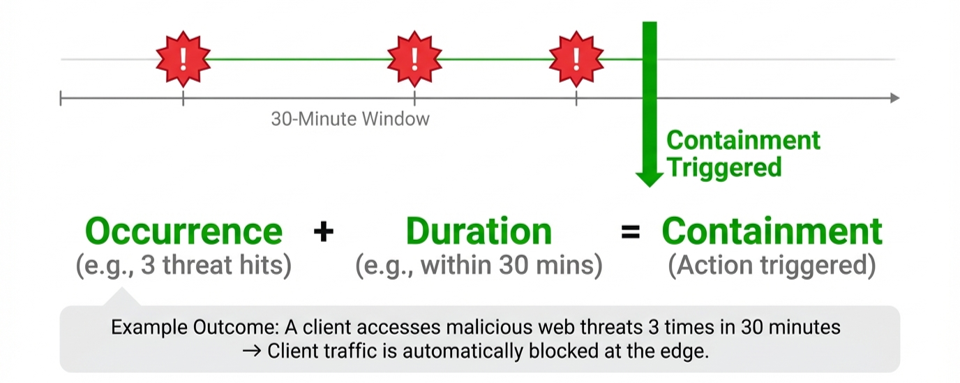
The "Three-Strike" Rule: Intelligent Thresholds vs. Alert Fatigue
One of the greatest contributors to staff turnover in SOC environments is alert fatigue. CDR combats this through a rule-based policy engine that uses "Occurrence" and "Duration" logic. For example, an MSP admin can configure a policy that only quarantines a device if it exceeds a threat threshold 3 times within a 30-minute window.
By implementing these intelligent thresholds, MSPs move from "firefighting" every single ping to managing meaningful security events, drastically reducing operational overhead.
Seamless Visibility: The Administrator’s Command Center
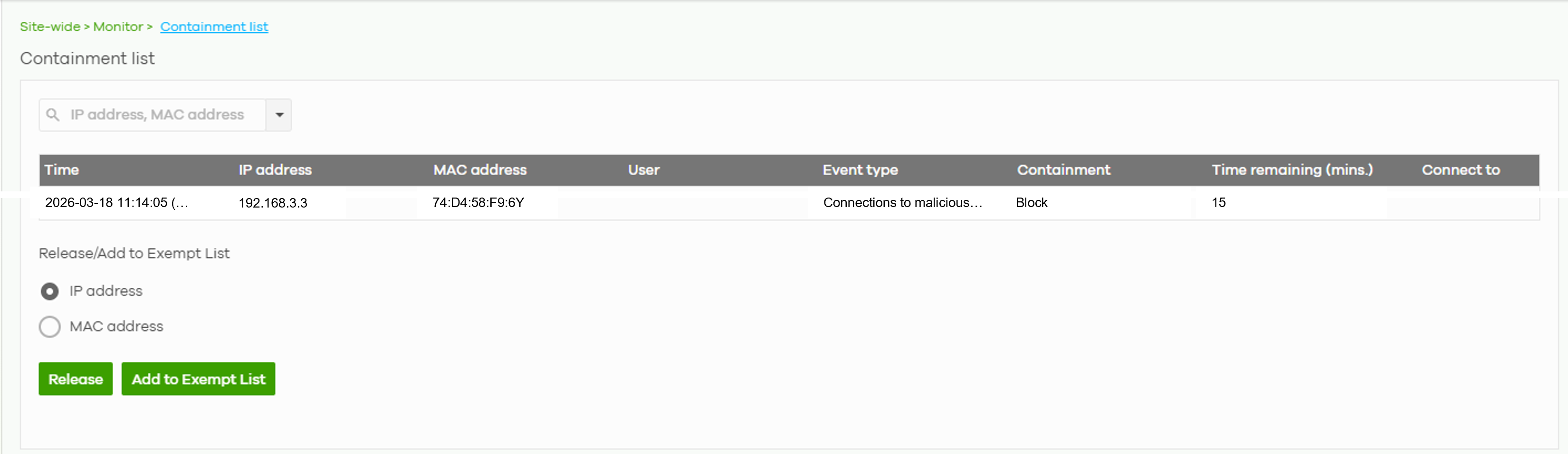
While the response is automated, the MSP retains absolute oversight. Within the NCC, the Containment List (Site-wide > Monitor > Containment list) serves as the centralized dashboard for all restricted devices.
From this command center, administrators can:
- Containment List
Monitor all isolated clients site-wide in real-time. - One-Click Release
Instantly restore network access for remediated devices. - Exempt List (Whitelist)
Input specific IP or MAC addresses to bypass CDR blocking for mission-critical infrastructure.
From Reactive to Proactive Management
CDR represents a fundamental evolution in how MSPs secure their clients. By transitioning from a reactive, manual response model to one of automated edge isolation, providers can offer a higher tier of security without a linear increase in headcount. The integration of Nebula firewalls and Nebula access points creates a unified defense-in-depth strategy that reacts at the speed of the threat, not the speed of the technician.
How to configure
📢 For a guide on CDR configuration process, check out our [How-To Article] below:
Categories
- All Categories
- 442 Beta Program
- 3K Nebula
- 228 Nebula Ideas
- 130 Nebula Status and Incidents
- 6.6K Security
- 641 USG FLEX H Series
- 357 Security Ideas
- 1.8K Switch
- 86 Switch Ideas
- 1.4K Wireless
- 54 Wireless Ideas
- 7K Consumer Product
- 303 Service & License
- 495 News and Release
- 93 Security Advisories
- 31 Education Center
- 10 [Campaign] Zyxel Network Detective
- 4.8K FAQ
- 34 Documents
- 88 About Community
- 110 Security Highlight