GEO-IP blocks internal LAN IPs
 Freshman Member
Freshman Member

Hi all!
Never solved this bad programmed feature: geo ip blocking is great but since the day introduced Zyxel never solved an important issue:
internal LAN IPs (lan1, lan2, dmz) are also checked for the country of origin, so now writing and this is an example:
190.168.x.x = Venezuela
194.166.x.x = Austria
191.168.x.x = Brazil
195.168.x.x = Slovakia
They are common IPs in use in SOHO ambients.
If you use the IPs in the example and set correctly the rules in the firewall as in this video: https://www.youtube.com/watch?v=uMv05II9VYs (and there is no other solution), firewall blocks all traffic!!!!
the video explains only one policy for the firewall section (any to any except Zywall), but there is another rule to set of course that is any to Zywall. But this doesn't change nothing cause if you use IPs on your lan that are the same countries they correspond, you obtain no traffic and also kicked off by the firewall interface.
You could tell me: change IPs on the lan side!!! Is not possible, cause IP blocks change and when they change, and you cannot expect it, you will be kicked by the firewall anyway till you change another time lan IPs.
Comments
-
Hi @hardstyler,
In the security policy rule, you can assign a specific zone in “From” and “To” to limit the source/destination IP coming from/to a certain “zone”.
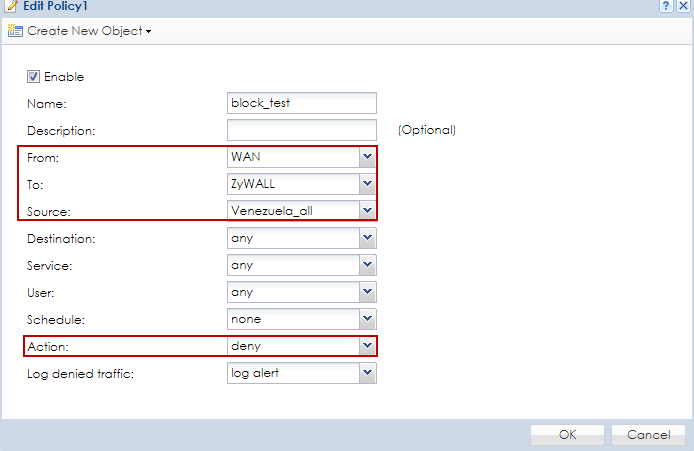
In the following example, create a address object with Venezuela.
Modify the IP address as 190.168.1.1 which belongs to Venezuela.
Create a security policy rule to block traffic from Venezuela to ZyWALL.
From: WAN, To: ZyWALL, Source: All Venezuela, action: deny
From one PC 190.168.1.2 in LAN1, it is still able to access the web GUI 190.168.1.1 successfully because the traffic if from zone “LAN1” and not “WAN”.
Hence, it doesn’t hit the block_test rule.
0 -
Solved, thank you!
0
Categories
- All Categories
- 442 Beta Program
- 3K Nebula
- 228 Nebula Ideas
- 130 Nebula Status and Incidents
- 6.6K Security
- 647 USG FLEX H Series
- 357 Security Ideas
- 1.8K Switch
- 86 Switch Ideas
- 1.4K Wireless
- 55 Wireless Ideas
- 7.1K Consumer Product
- 304 Service & License
- 496 News and Release
- 93 Security Advisories
- 31 Education Center
- 10 [Campaign] Zyxel Network Detective
- 5K FAQ
- 34 Documents
- 89 About Community
- 110 Security Highlight
 Zyxel Employee
Zyxel Employee