WWW drop all ! access by user
 Freshman Member
Freshman Member
good morning
I have the following need. We have just installed our Zyxel Zywall USG60 with two isp with failover. Everything works perfect.
But I have the need for my local network users (lan1), to access specific websites. But not all users can browse all internet sites.
I tried to create an object and block websites by fqdn and it works very well ...... but really what I need is to close all traffic from lan1 to wan, by http / www, and somehow be able to enable each ip or user (I have connected the zywall to the AD windows of lan1), only the urls that have permission to use.
Is there any way I can do it?
thanks for your help
Oscar
All Replies
-
Hello @DivisionAzul and welcome to the forum!
So I understood your request right that you would like to have two firewall rules?
One rule that denies access to the internet for the whole LAN network, but one rule above this that should allow access into the internet for specific clients?
You can change the rule LAN2-to-Any to something like this:
You are quite flexible with your criteria, so you can for example use static DHCP for the clients allowed to the internet, put them into an address group object and use them in your security policy.
You can also make it more strict by defining that they can only access a specific destination.
The default deny rule at the bottom will already take care of blocking internet access for the other clients.
BUT BE AWARE: LAN2 might not have access to LAN1 and other firewall zones anymore when changing the LAN2-to-Any rule. So depending on your network you might need more firewall rules.
Best regards
Lukas
0 -
Good morning and thanks for your help.
I really like your solution, I explain the situation.
My network structure is simple, wan1 (isp1) wan2 (isp2) with failover, wan1 master.
Lan1: 192.168.0.0/24
All my users / computers have static ip, therefore, I create an object for each static ip, to use it as ipv4 source, .... the problem is that each static ip has to have different groups of Internet-accessible urls , from lan to wan, .... What is the problem? that when I create an FQDN object, to allow access to a specific url, it only allows me to create 1 FQDN per 1 object, ... if a user has to have access to 20 urls ... I would have to create 20 FQDNs, and add 20 rows to the firewall .....
My first question, how can I create a group of "websites-fqdn-ipx" urls for example to have a single line in the firewall for each static ip
Currently until you read your answer today, I have two users in tests, I show you what I have in security policies
I have created a UTM profile for each user in this case, and within the profile, I have created a personal profile for these users in a content filter.
In category service I have everything marked and in BLOCK
In personalized service, I mark the option "allow web traffic ONLY for trusted websites" and proceed to manually add each of the URLs for that user
At the moment this solution is what I thought, and I am in tests, but it works, I have a problem, in some destination urls like Facebook, the images do not load correctly, youtube, does not load the videos, some other websites work perfect, I have Check the box allow java / Activex ......
I think your solution is more correct. But I have the doubt of how to create a group of Fqdns to not apply to a single user / ip
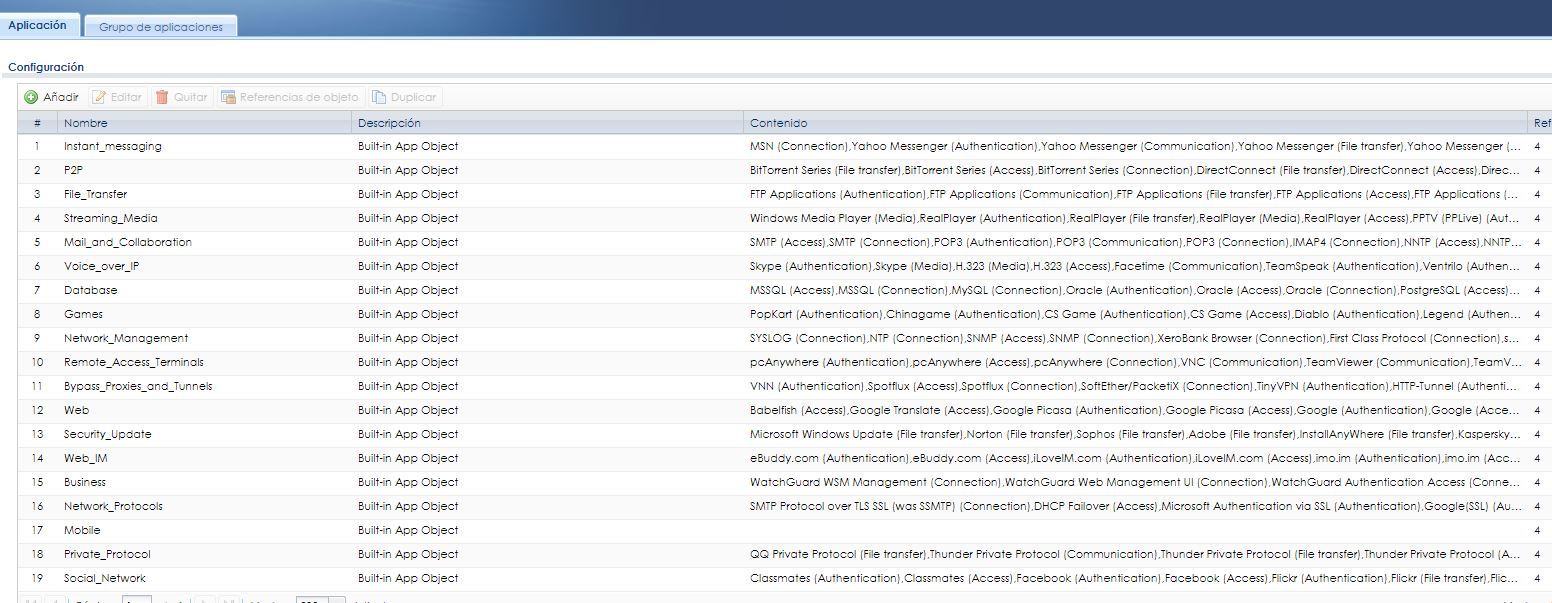
Another option I've seen in the zywall is in Objects, "Application" I see objects like
I don't know if with this I could solve those loading problems of some web areas like the ones I commented that don't work well, on the other hand I don't know how to add an application as an object to the control of policies.
These are all my doubts.
Thank you very much for your support.
0 -
Hello @DivisionAzul,
I just simply wanted to show the options possible. I was not aware about the requirement that you have two different groups of IPs in your LAN. I was also not aware of Content Filter.
So in that case you will have to use at least two firewall rules, one for each group.
Please be aware that having such strict firewall rules will always have a noticeable impact. You will from time to time notice that specific things are not working, which you will have to allow again.
And these services or destinations will add up from time to time.
So maybe better stick to the default firewall rule LAN-to-Any allow and use the Content filter to block what is not appropriate for the LAN?
Maybe also have a look here regarding Content Filter configuration:
Regarding FQDN I had no issues to put multiple FQDNs into a group. Please note that these firewall rules are just simply examples how such a configuration could look like (and I would rather suggest the approach to use the default firewall rule and Content Filter):
I hope this helps.
If not, we can also take the conversation further per private message.
Best regards
Lukas
1
Categories
- All Categories
- 442 Beta Program
- 3K Nebula
- 223 Nebula Ideas
- 129 Nebula Status and Incidents
- 6.6K Security
- 638 USG FLEX H Series
- 357 Security Ideas
- 1.8K Switch
- 86 Switch Ideas
- 1.4K Wireless
- 54 Wireless Ideas
- 7K Consumer Product
- 301 Service & License
- 494 News and Release
- 93 Security Advisories
- 31 Education Center
- 10 [Campaign] Zyxel Network Detective
- 4.8K FAQ
- 34 Documents
- 88 About Community
- 109 Security Highlight