PCI Compliance Deny X-Frame-Option
Hi,
Have a USG20W and have failed PCI Compliance due to click jacking vulnerability.
I have already attended to a TLS issue and this was resolved through CLI.
It appears to be the router login screen that when the IP is input that needs to have its X-Frame-Option set to deny. Can anyone please point me in the right direction or provide method (as I found with the TLS issue) that will allow me to rectify this.
Thanks in advance
All Replies
-
Upgrade the device to V4.32 and later versions and try the commands.
Router(config)# ip http x-frame-options
Router(config)# write
0 -
Hi Jasailafan,
Current firmware is currently already 4.35 so can I assume that the above can just be entered via CLI?
Also, can I confirm if "ip" in the above string is my office IP address and that I should enter that in place of "IP" as you have detailed in your post.
also, I'm assuming that the operator will be needed after the line "write"
I.E Deny or SameOrigin etc.
Very grateful for your input here really appreciate it.
Dean
0 -
If the firmware version is already 4.35, just copy and paste the commands.
The "ip" in the command is the command itself. You don't need to replace it with your IP address. Just copy the whole command "ip http x-frame-options".
0 -
Thank you
Will try this but just so I understand, this script will do what exactly?
My understanding is that the change needs to be that X-frame-options needs to be "set" to "deny" or "Same Origin" as opposed to what it seems to be at the moment which, by elimination must be "allow" From this I assume that there would be a different syntax for each which would effect whatever option is needed.
Many thanks again.
Dean
0 -
Hi @HoS,
Enable x-frame-options header
Router(config)# ip http x-frame-options
Router(config)# write
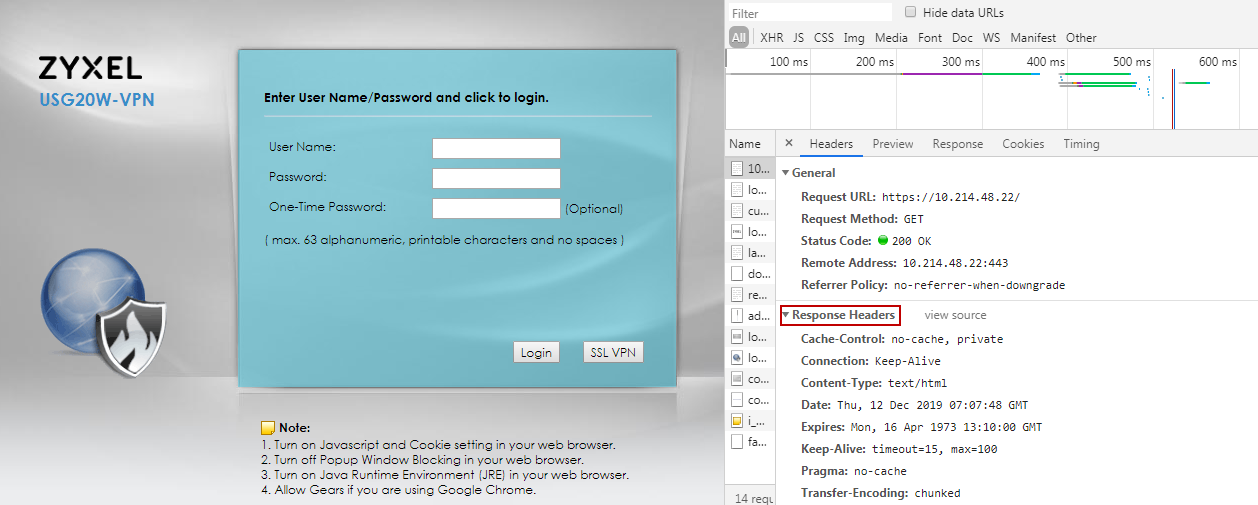
When the commands are entered, X-Frame-Options: SAMEORIGIN is added to the HTTPS response header.
Disable x-frame-options header
Router(config)# no ip http x-frame-options
Router(config)# write
0 -
Hi Emily,
This is fantastic. So helpful seeing the actual screenshots.
Thank you to Jasailafan also. Really appreciate your time and effort.
Was beginning to think this was in impossible thing to do !
Given that it's quite a fundamental business issue I have to say I'm a little
surprised it isn't documented a bit more.
Anyway. Just one last question, The setting is clearly noted in the header with Same Origin.
I understand this will also be acceptable from PCI compliance company comments but wonder, given there seems to be options of Deny, Same Origin and allow. Is there anything different that would have to be entered to make explicit commands like this or is the only option same origin with this particular device?
Anyway, thanks again. Really grateful :-)
0 -
Hi @HoS,
The major purpose of this header option on device is to prevent clickhijack.
The SAMEORIGIN is the best option on ZyWALL to prevent clickhijack, so we implement this option only on ZyWALL.
It has more flexibility for user's web sites in the same domain name space to embed device pages by iframe than the option "DENY".
Besides, ZyWALL is not a web site to provide contents for others, so we don’t support the option “ALLOW-FROM”.
0 -
Hi I am getting this come up on our recent PCI scan for our Zywall USG 310 so opened up the web console to type the following commands in:
Router(config)# ip http x-frame-options
Router(config)# write
As soon as I pasted in the first command "ip http x-frame-options" into the console everything froze and the router stopped working. Luckily it rebooted itself a few minutes later and people could continue to work! How can I make this change without this happening? I am using firmware version V4.64(AAPJ.0) / 2021-06-26 00:00:26.
0 -
Hi can anyone help it seems odd that that command would crash the router, I checked the logs and the router rebooted itself shortly after I entered it. Could it be because I entered the command using the web console in the browser rather than using a proper SSH connection from Putty?I am nervous of trying to run it again now as we are working remotely and there is no one there to power cycle the router. Also on another note, why do the firmware release notes say that it is a MUST to physically power the router on and then off again at the switch after an update. If that is the case what is the point of the automatic firmware update feature?0
-
Hi I was able to run the command successfully from a proper SSH window using Putty with no ill effects. Perhaps the router crashed because I was using the web console so wont use that again.
0
Categories
- All Categories
- 442 Beta Program
- 2.9K Nebula
- 220 Nebula Ideas
- 128 Nebula Status and Incidents
- 6.5K Security
- 608 USG FLEX H Series
- 347 Security Ideas
- 1.7K Switch
- 84 Switch Ideas
- 1.4K Wireless
- 52 Wireless Ideas
- 7K Consumer Product
- 299 Service & License
- 482 News and Release
- 92 Security Advisories
- 31 Education Center
- 10 [Campaign] Zyxel Network Detective
- 4.8K FAQ
- 34 Documents
- 87 About Community
- 105 Security Highlight
 Freshman Member
Freshman Member


 Master Member
Master Member


 Zyxel Employee
Zyxel Employee