Zywall USG FLEX Series & ATP Series - V5.42Patch 0 Firmware Release
 Zyxel Employee
Zyxel Employee



Zywall USG FLEX Series & ATP Series Release Note
February 2026
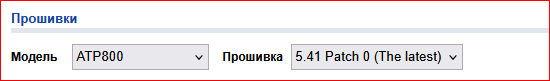
Firmware Version on all models
(Click the hyperlink to find the firmware file directly)
| FLEX Series | Download link | ATP Series | Download link |
| FLEX50 | removed | ATP100 | removed |
| FLEX50W | removed | ATP100W | removed |
| FLEX50AX | removed | ATP200 | removed |
| FLEX100 | removed | ATP500 | removed |
| FLEX100W | removed | ATP700 | removed |
| FLEX100AX | removed | ATP800 | removed |
| FLEX200 | removed | ||
| FLEX500 | removed | ||
| FLEX700 | removed |
New Feature and Enhancements
| New Feature and Enhancements | S | C |
| 1. Anti-Malware allow/block list supports SHA-256 hash value. | V | - |
| 2. [eITS#250801365] Enhanced the format of the Security Policy alert email to improve readability. | V | - |
| 3. [eITS#250901370] Support # and ; as a comment symbol in External Block List (EBL) entry. | V | - |
| 4. Local GUI updated the i-note content for ‘Change to a Different ISP’ in cloud mode. | - | V |
Bug Fix
| Bug fix | S | C |
| 1. eITS#250601128 a. Fix: Unexpected reboot when IPS is enabled. | V | - |
| 2. eITS#250701806 a. Fix: A specific FQDN object is not taking effect in the destination of IP Exception. | V | - |
| 3. eITS#250800047 a. Fix: Disabled Airtime Fairness or Overwrite Full Power settings are not saved to the startup-config.conf file and are unexpectedly re-enabled on APs after the controller is rebooted. | V | - |
| 4. eITS#251001535 a. Fix: It is impossible to configure virtual interface IP after ATP800 is upgraded to 5.41. | V | - |
| 5. eITS#251001984, 251100309 a. Fix: Traffic blocked due to IP-MAC binding table sync issue. | V | - |
| 6. eITS#251002189 a. Fix: DHCP does not work for Built-in AP. | V | - |
| 7. eITS#251201472 a. Fix: SSL Inspection is unable to flush old session and caused concurrent session is increasing until full. | V | - |
| 8. Common vulnerabilities and Exposures: ZLD5.42 Patch0 is no longer vulnerable to the following CVE References: ⚫ CVE-2025-11730 | V | V |
Please refer to the Download Link for more details.
Comments
-
Ya'll botched it again.
Device wont load config from 5.41 and reset to default. Now a 2 hour drive after hours…
Thanks!
0 -
Sorry to read your bad experience, @MikeForshock. Would you kindly share some information about this device misbehave?
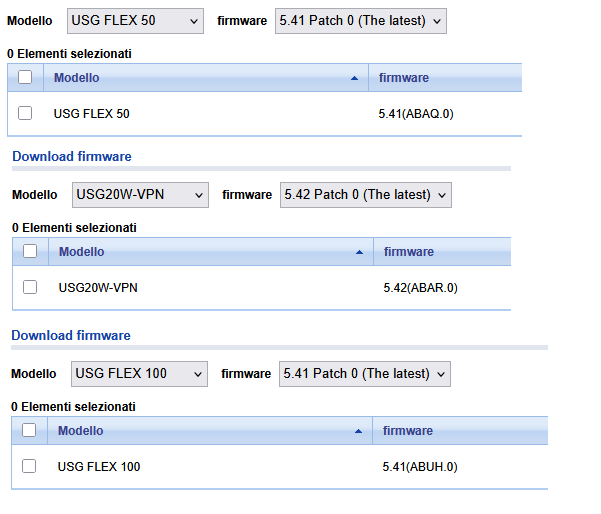
Edit: some devices do not see into update 5.42 firmware, only 5.41.
This apply to USG Flex 50, USG Flex 100, but not on USG-VPN 20W. This is also reflected on MyZyxel as available firmware.Links above are not working for these models.
Last edit:
Due to this occurencies…
https://community.zyxel.com/en/discussion/32291/atp200-no-connection-to-gateway-after-automatic-firmware-update-v5-41-to-v5-42
Update has been pulled out?
0 -
Why you don't update topic and don't create new, that already this great release was rollback?
1 -
There's are the things that are not satisfying to me in this occurence:
1: a security update is released but is specified in this announcement only at the bottom…
2: a security update is release at thursday, which might be a good thing for allowing a weekend massive update, but on the other hand have a really small check-in period
3: delivered issues from end users on some devicesAnd after 3 days not even a "sorry for the issue, release paused, we are looking into it".
These devices are 24/7 working (older versions did not have power switch) and gateway for securing networks and I am aware that most of the development efforts are on Flex H series.
However communication should be better than this, this is also addressing a CVE vulnerability. Caring should be part of the development.0 -
Hi @alexey
Thank you for your feedback, and we apologize for the delayed communication on this matter.
The V5.42 Patch 0 firmware has been temporarily withdrawn while we address the reported issues. A date code firmware has been prepared to resolve the problem, and it has already been provided to you. Please let us know if you encounter any further issues after applying it.
We have noted your feedback regarding our communication process and will work to improve. Thank you for your patience.
Zyxel Melen0 -
Hi @mMontana
Thank you for your detailed and constructive feedback. Your concerns are completely valid, and we owe the community a better response.
The V5.42 Patch 0 firmware has been temporarily withdrawn. A date code firmware has been prepared to address the reported issues, and we will send it to you via private message shortly.
We have taken note of your feedback on our release communication and will bring it to the team internally. Thank you for your patience and your continued support of this community.
Zyxel Melen0 -
Sorry, @Zyxel_Melen also this was not addressed.
USG20W-VPN/USG Flex 50W still have available 5.42 firmware on MyZyxel platform; I have updated a device which is still working without perceived issue.
This is the "final" 5.42 firmware for this device? Or also this firmware will be superseeded from the coming one?
0 -
I'm far from delighted to see a 6:53AM CET post about a Flex H release… And not a word from Zyxel on this thread. I know it's not something on the personal writing in this community, but seems gaving a touch o perspective about where the attention is.
0 -
Hi @mMontana ,
Apologies for the delayed response, and thank you for your patience.
To clarify the firmware situation: V5.42 Patch 0 was intended to be removed, but due to a system error, it remained available on the myZyxel portal for USG20W-VPN and USG Flex 50W. We apologize for the confusion this caused.
The good news is that V5.42 Patch 1 has been released today (February 11). This is the version we've been working on after pulling Patch 0, and it supersedes the previous release. We recommend upgrading to Patch 1 at your earliest convenience.
Zyxel Melen0 -
Thanks for the hard work of the developers for solving the issues in version 5.42 P0 and the release 5.42 P1
However, after the botch of the files available 4th of February… how I could be possibily confident for a safe update?
I was lucky enough saturday to arrive "late" for the earliest release (which whas thursday, in my time zone) and version 5.42 P0 was already pulled out of distribution. I was double lucky to deploy 5.42 P0 on a device that worked even 3 days without hiccups.
How I know, less than 6 hours from the release, that something was not botched again?0
Categories
- All Categories
- 442 Beta Program
- 3K Nebula
- 222 Nebula Ideas
- 129 Nebula Status and Incidents
- 6.5K Security
- 619 USG FLEX H Series
- 349 Security Ideas
- 1.7K Switch
- 84 Switch Ideas
- 1.4K Wireless
- 53 Wireless Ideas
- 7K Consumer Product
- 298 Service & License
- 486 News and Release
- 92 Security Advisories
- 31 Education Center
- 10 [Campaign] Zyxel Network Detective
- 4.8K FAQ
- 34 Documents
- 88 About Community
- 105 Security Highlight
 Ally Member
Ally Member


 Guru Member
Guru Member


 Master Member
Master Member