How can the inbound destination NAT be used to hide the server’s real IP via a VPN tunnel?
Options
Zyxel_Charlie
Posts: 1,034  Zyxel Employee
Zyxel Employee




 Zyxel Employee
Zyxel Employee



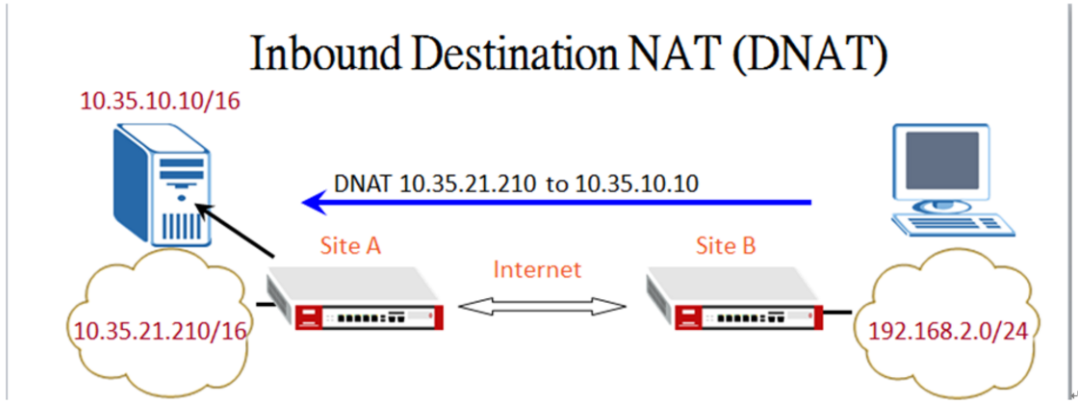
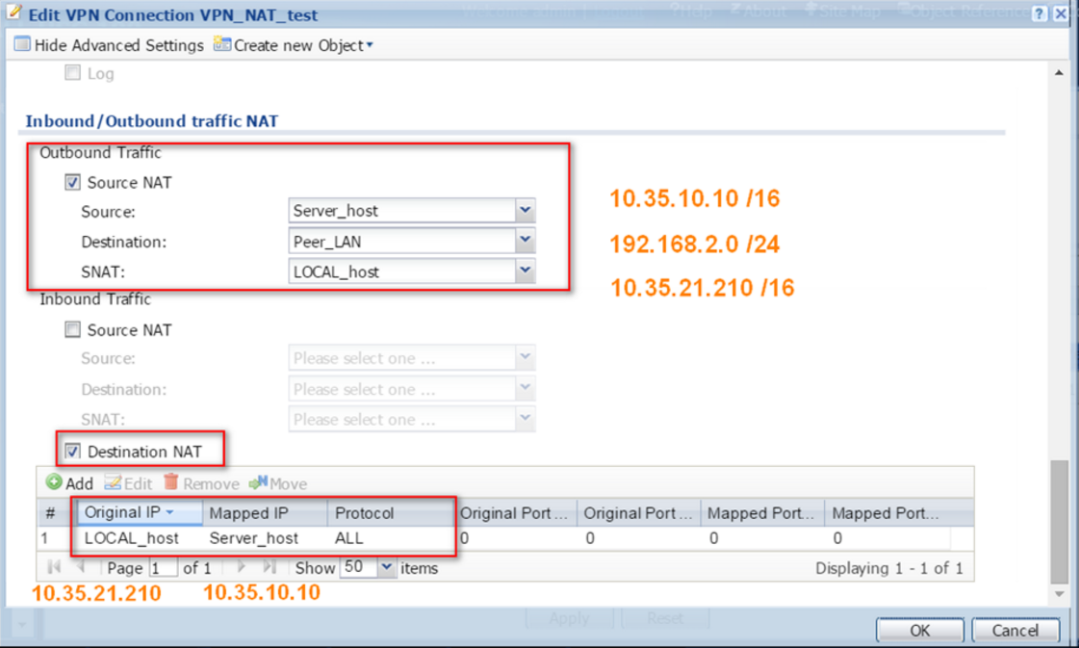
A customer requires that the server’s real IP is hidden when using site-to-site VPN. This can be done by using an inbound destination NAT to hide the server’s real IP when VPN is established.
The inbound DNAT works as a virtual server.
It can redirect the VPN traffic to the internal server.
Steps:
VPN connections:
Tagged:
1
Categories
- All Categories
- 442 Beta Program
- 3K Nebula
- 224 Nebula Ideas
- 130 Nebula Status and Incidents
- 6.6K Security
- 640 USG FLEX H Series
- 357 Security Ideas
- 1.8K Switch
- 86 Switch Ideas
- 1.4K Wireless
- 54 Wireless Ideas
- 7K Consumer Product
- 303 Service & License
- 494 News and Release
- 93 Security Advisories
- 31 Education Center
- 10 [Campaign] Zyxel Network Detective
- 4.8K FAQ
- 34 Documents
- 88 About Community
- 109 Security Highlight