Double NAT problem USG20W-VPN
Hello,
I'm getting nowhere with my double NAT problem and I need your help.
I have the following structure, which I cannot realize otherwise.
How can I realize that I can access the server behind the USG from the address range 192.168.2.0?
I would also like to know how I can disable the log for port up/down.
Thanks for your help!
Accepted Solution
-
Can you make the USG20W your main router? or use a bridge on the USG20W?
Their might be a way to not double NAT if the FritzBox does static route then do a routing rule on the USG20W with next hop gateway 192.168.2.1 and Source Network Address Translation to none.
Have you setup any Virtual Server rules?
6
All Replies
-
here is the right plan
0 -
Can you make the USG20W your main router? or use a bridge on the USG20W?
Their might be a way to not double NAT if the FritzBox does static route then do a routing rule on the USG20W with next hop gateway 192.168.2.1 and Source Network Address Translation to none.
Have you setup any Virtual Server rules?
6 -
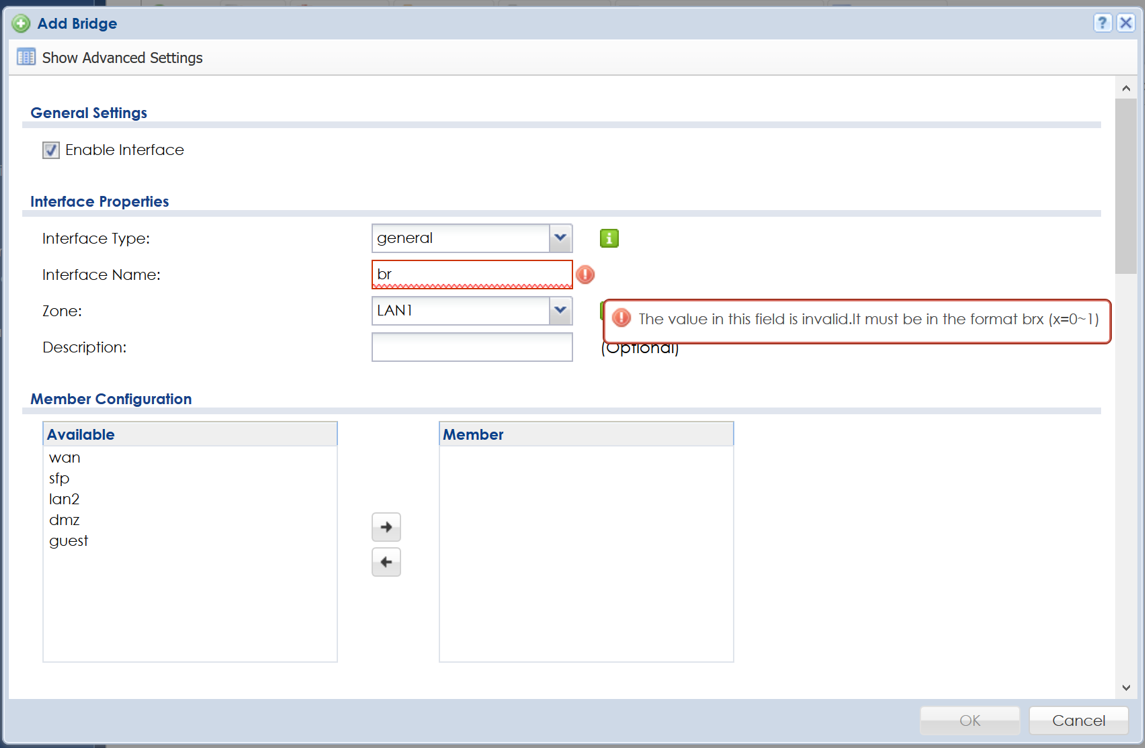
USG as main router is unfortunately not possible. Bridge does not work either, see screenshot. How can I fix the bridge problem?
In the fritzbox I set a static route and in the USG the NAT accordingly. Now it works THANK YOU
0 -
For the Bridge you put in br0 then then the members like WAN and DMZ but if you got statc route to work no need.
1 -
Hi @bdb
it looks like, you are useing the fritzbox for VoIP and router from your ISP.
As already mentioned by @PeterUK , you should be able to config a routeing rule at the fritzbox, that forward all traffic from 192.168.1.x to 192.168.1.1 (WAN interface USG20).
At the USG20 you had to disable the SNAT to forward the traffic to the fritzbox and avoid double snat first.
Regards
Chris
1 -
Hi @bdb
You can disable default snat at “CONFIGURATION > Network > Interface > Trunk”
BTW, you have to add static route on upper layer router for subnet 192.168.1.X/24.
Click “Show Advanced Settings” and untick “Enable Default SNAT”
0 -
Hi,
first of all thank you for your help.
Yes, i use from the FritzBox VoIP and ISP.
disabling Enable Default SNAT alone does not help.
Under "Default Truk Selection" I don't have to set anything?
With the USG20 I enter the following under Static Route:
IP: 192.168.1.0 (the IP range of the USG?)
Do I then enter a gateway or do I select the WAN interface?
0 -
Hi together,
disableing the SNAT is only one part and do not fix the double SNAT as described.
In your case
All traffic from the Devices, that are attached to the USG is by default routed trough the WAN Port to the FritzBox -> that's by default working.
You have to tell the FritzBox (by static route settings) where the reply package for the Subnet(s) on your USG should send to - in your case - IP-Subnet 192.168.1.0/24 should be send to the WAN-IP of the USG.
If you require a connect to the FritzBox Network, make a static route on the USG and configure the FritzBix Subnetz (Gateway) to get connected to your fritzBix Webinterface.
Good Luck
Chris
0 -
So far I have set a static route in the FritzBox:
192.168.2.0 (IP)
192.168.2.10 (USG)
And a NAT rule in the USG:
Virtual Server
WAN - ext.IP (192.168.2.0)
LAN - int.IP (Server 192.168.1.50)
Release for corresponding services
A security policy:
For the services of the server
From the network of the Fritzbox (192.168.2.0) I get access to the services of the server.
Other settings failed so far.
But this doesn't work:
IP-TV of the Fritzbox I can't get into the network of the USG. According to the log the default rule blocks the traffic from 192.168.2.1 to 224.0.0.1 (probably a mulicast service).
I tried different security guidelines but the firewall always drops.
I also can't get a VPN connection to the USG.
I activated the port forwarding in the FritzBox accordingly in the log but always no proposal chosen.
0 -
Hi @bdb
IPTV require IGMPv2/3 support by the firewall/router device.
can you please verifiy, what USG devices are supporting IGMP v2/3 regular by ZYXEL ?
Here the config in a example (please change the IP as required for your infrastructure):
USG
WAN1-IP 192.168.2.1/24
Static route - 192.168.2.0/24 next hop (FB-IP)!
SNAT-disabled!
Fritzbox
FB-IP 192.168.2.2
Static route - 192.168.1.0/24 next hop 192.168.2.1 (WAN1-IP)!
Good luck
Chris
0
Categories
- All Categories
- 442 Beta Program
- 3K Nebula
- 228 Nebula Ideas
- 130 Nebula Status and Incidents
- 6.6K Security
- 648 USG FLEX H Series
- 357 Security Ideas
- 1.8K Switch
- 86 Switch Ideas
- 1.4K Wireless
- 55 Wireless Ideas
- 7.1K Consumer Product
- 304 Service & License
- 496 News and Release
- 93 Security Advisories
- 31 Education Center
- 10 [Campaign] Zyxel Network Detective
- 5K FAQ
- 34 Documents
- 89 About Community
- 110 Security Highlight
 Freshman Member
Freshman Member


 Guru Member
Guru Member



 Ally Member
Ally Member


 Zyxel Employee
Zyxel Employee






